Signing in users with OAuth v2
To enable user sign-in using OAuth 2.0 and ensure a smooth conversational experience, follow the steps below. This process includes the latest updates for automated session management and timeout handling.
Configuration Steps
To enable user sign-in using OAuth 2.0, follow these steps:
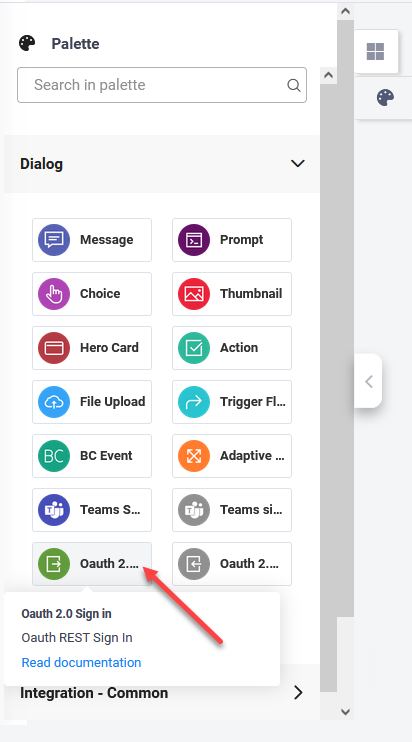
- From the Flow Palette, Dialog section, drag the Oauth 2.0 Sign in step and drop it within the flow where you want to perform the OAuth v2 sign in.
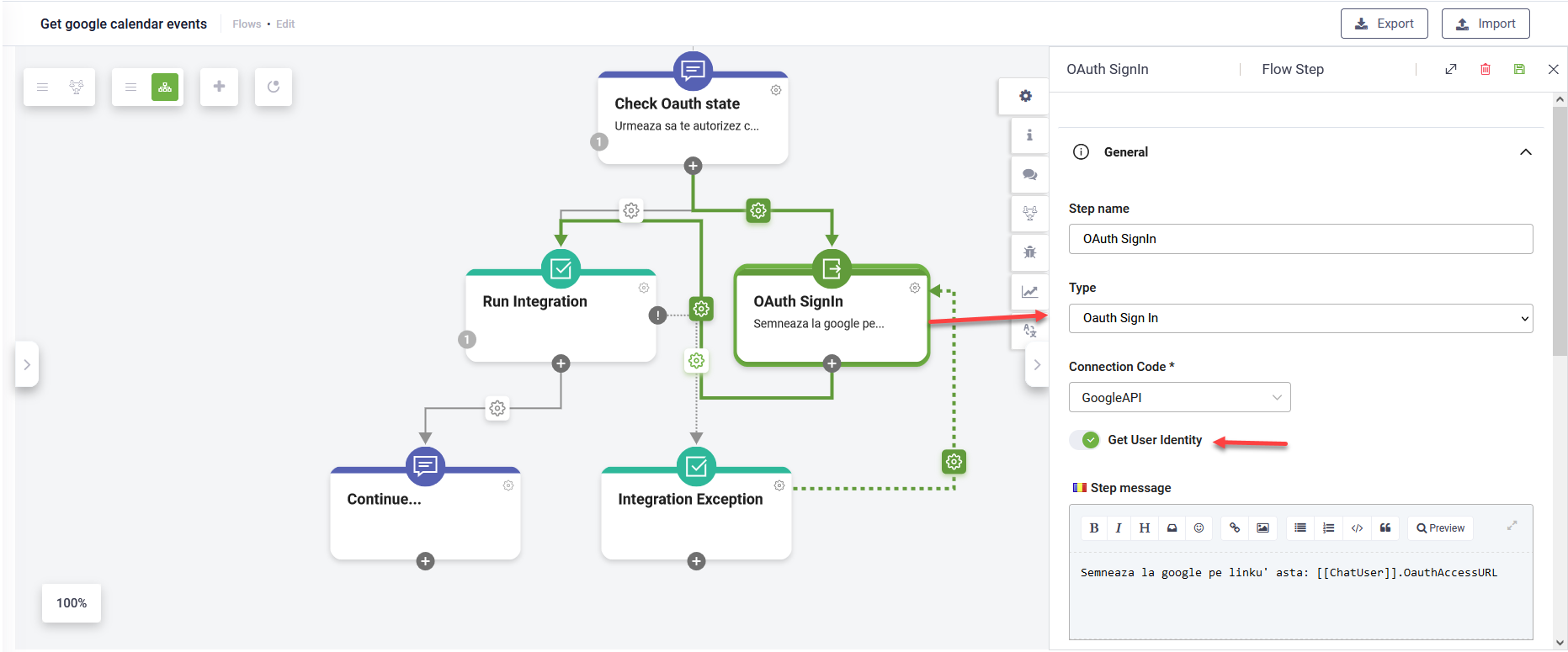
- Provide a flow step name.
- From the Connection Code field, select the connector app you created for OAuth v2 authorization.
- In the General section, turn the Get user identity toggle on.
- In the Metadata section, tap on Block user input. By default, the sign-in step is rendered as a hero card.
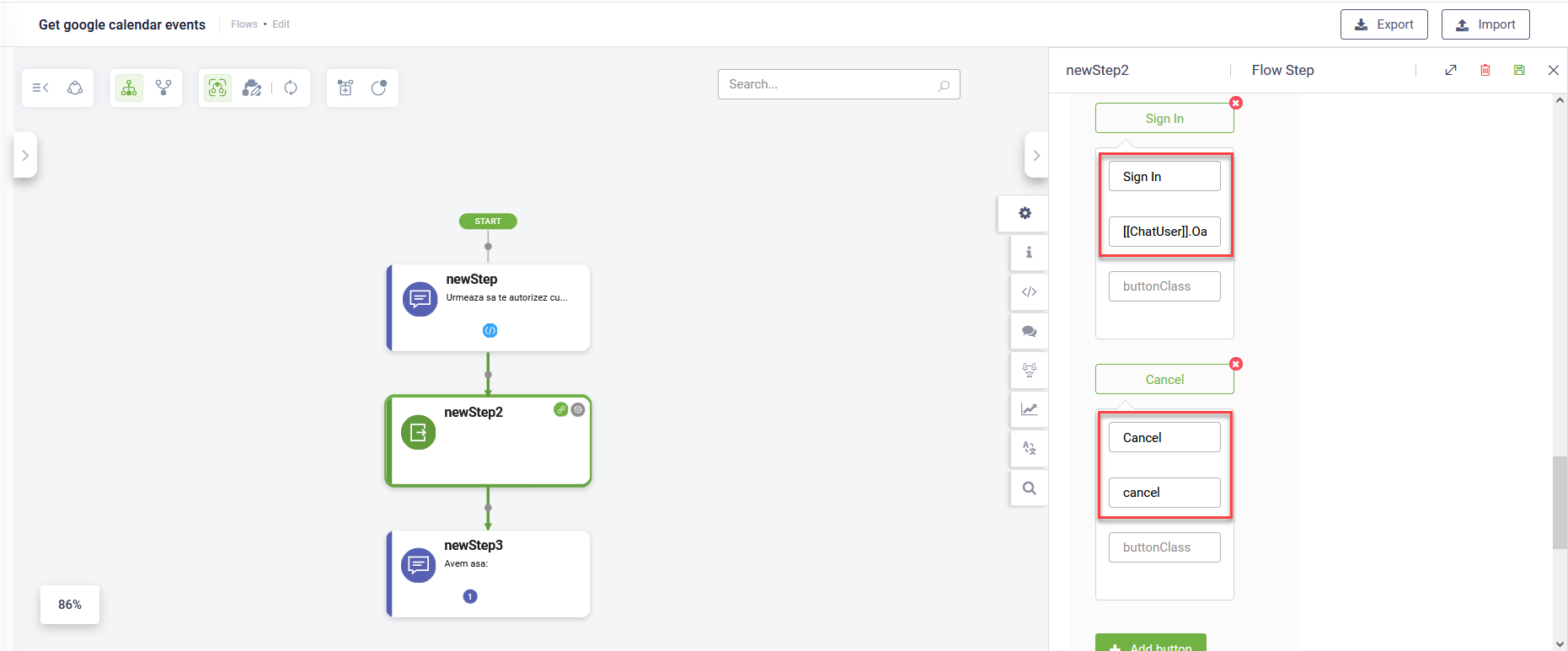
- Configure the hero card with the following buttons:
- Sign In - Set the value to: [[ChatUser]].OauthAccessURL.
- Cancel - Set the value to: cancel.
- Save the step to apply the changes.
Continue designing your flow with actions the assistant should perform on user’s behalf after getting user’s authorization.
When the OAuth 2.0 Sign in step runs, the user's identity metadata will be stored in the [[ChatUser]] entity. This mapping is based on the response configuration in the Get User Identity connector action.
After this step, continue with Druid-specific authentication using actions such as: SaveIdentifiedUser and SaveAuthenticatedUser. These can be configured either in the next step of the flow or in the PostActions section of the SSO Sign In step.
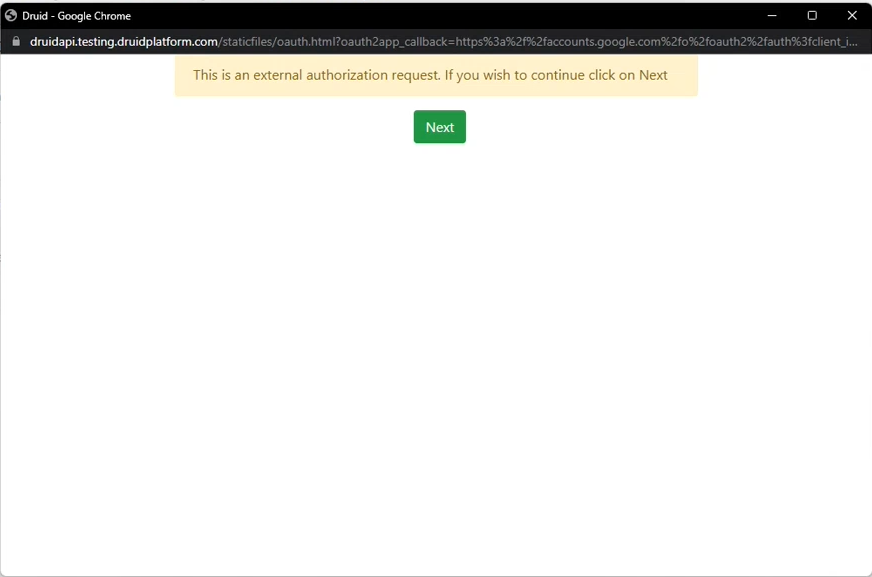
At runtime, when the user clicks the Sign in button/link, Druid redirects the user to a Druid hosted page (the login/consent page at the WEB API service). Example:
After the user confirms the authorization, the first special action in the OAuth App is automatically invoked and the authorization process completes, meaning that the access token will be saved in the conversation context and used on any integration which consumes that specific OAuth App. The AI Agent will further perform the actions on user’s behalf as set in the conversational flow.
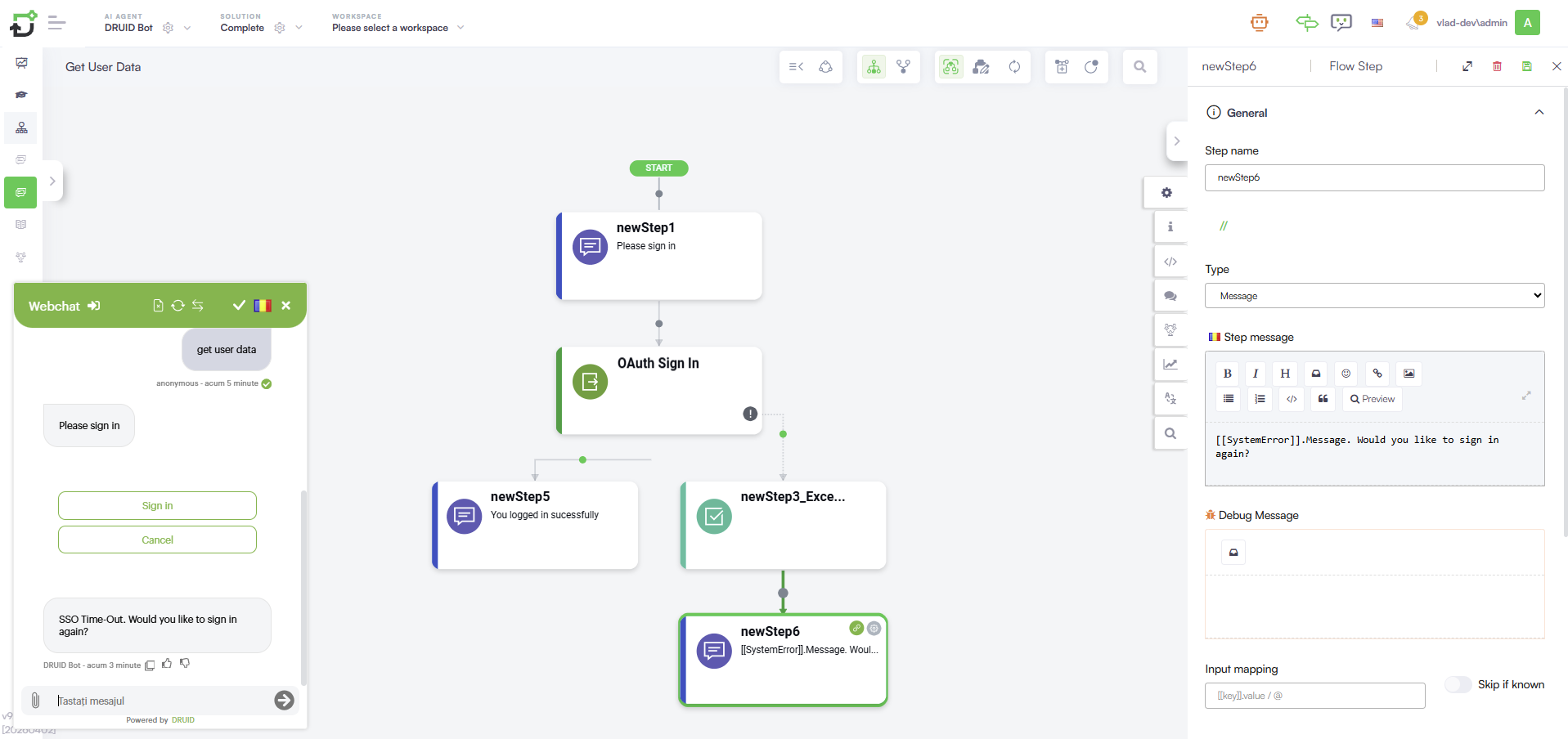
Authentication Timeout Management
To prevent the conversation from becoming unresponsive if a user does not complete the sign-in process, the Flow Engine includes an automated timeout mechanism. This ensures the flow does not remain blocked until the user manually selects Cancel.
How it works
The authentication session is active for 120 seconds from the moment the sign-in link is generated in the chat. If the user fails to authenticate within this window:
- The system triggers a failure state instead of remaining stuck in the sign-in step.
- The Flow Engine raises a specific exception that can be caught and handled within the flow.
Handling the Timeout Exception
To manage the conversation path when a SSO timeout occurs:
- Open the OAuth 2.0 Sign in step and go to the Metadata section.
- Enable the Exception Handler.
- Create a flow path for when the exception is raised. Recommended actions include:
Signing in users with OAuth v2 best practices
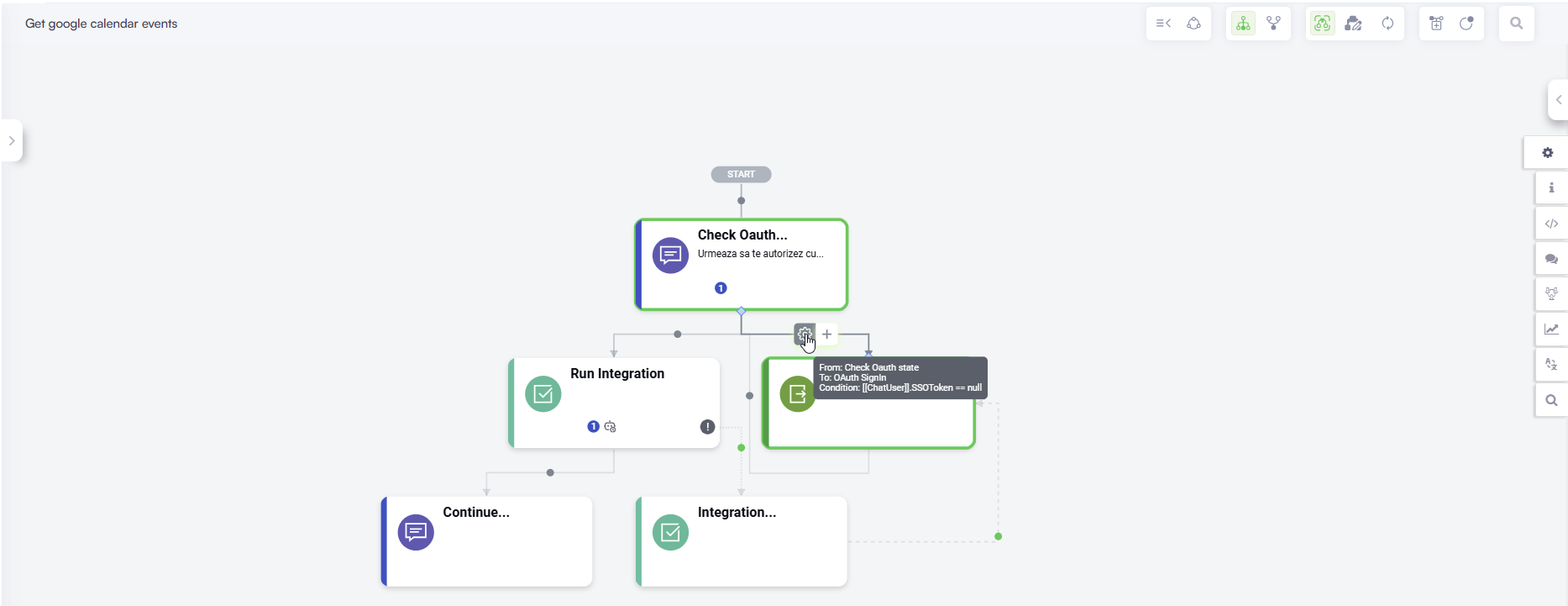
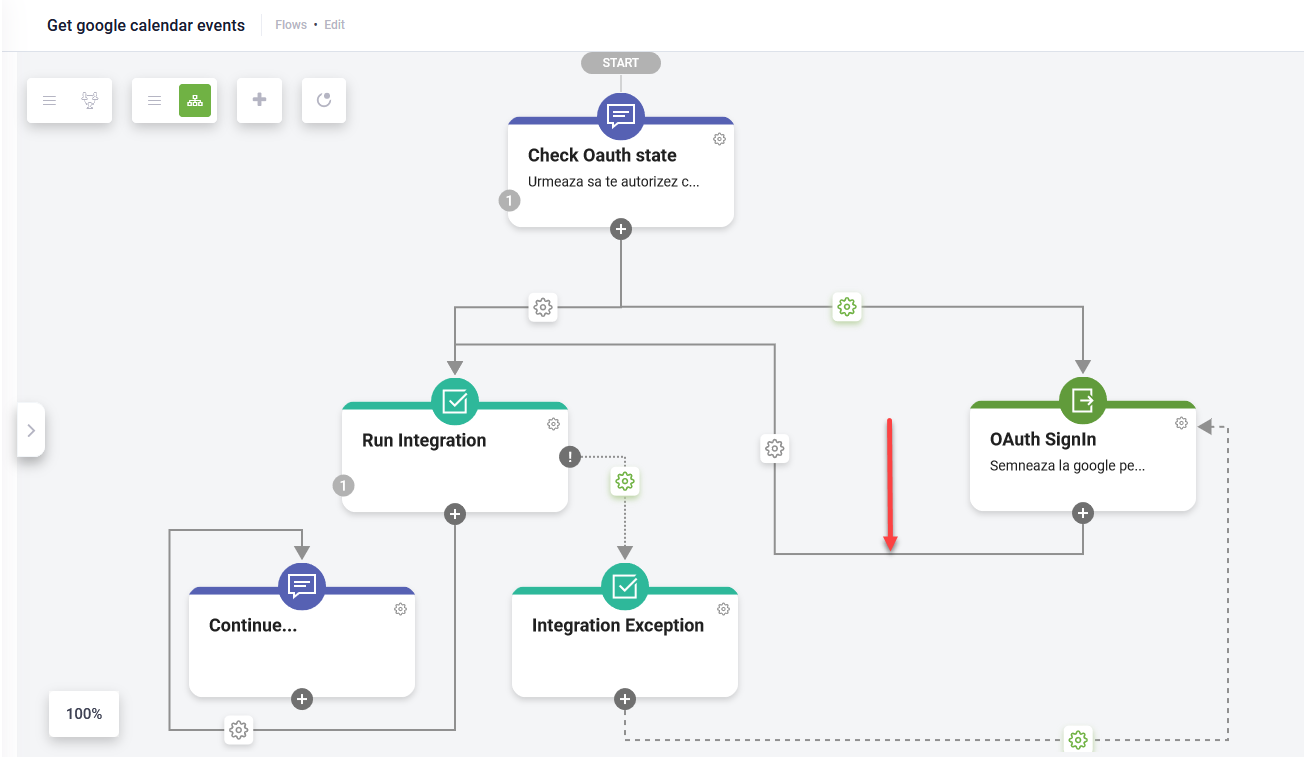
Use these best practices to ensure that the access token used to authorize server-to-server API calls is handled correctly:
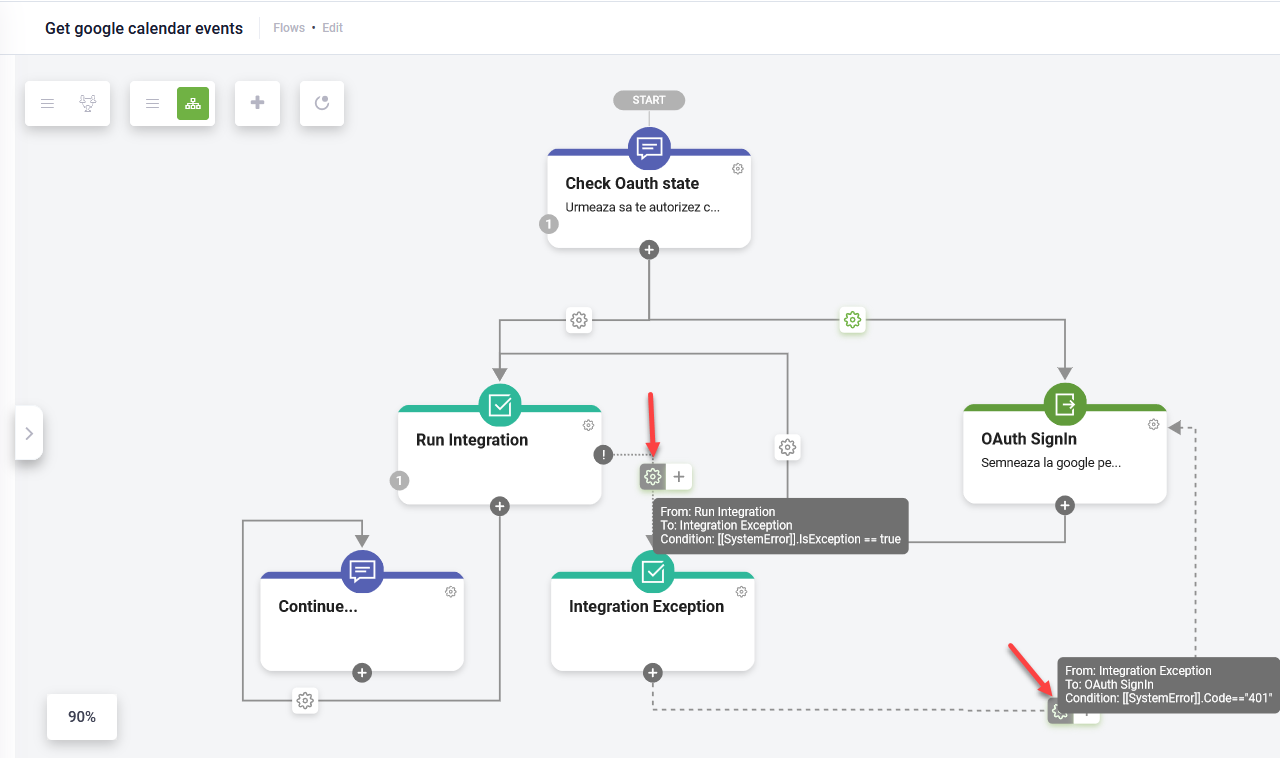
- Set condition to execute the Oauth 2.0 Sign in flow step (the one you configured at step 4 above) only if [[ChatUser]].SSOToken == null.
- After executing the Oauth 2.0 Sign in flow step, run the integration.
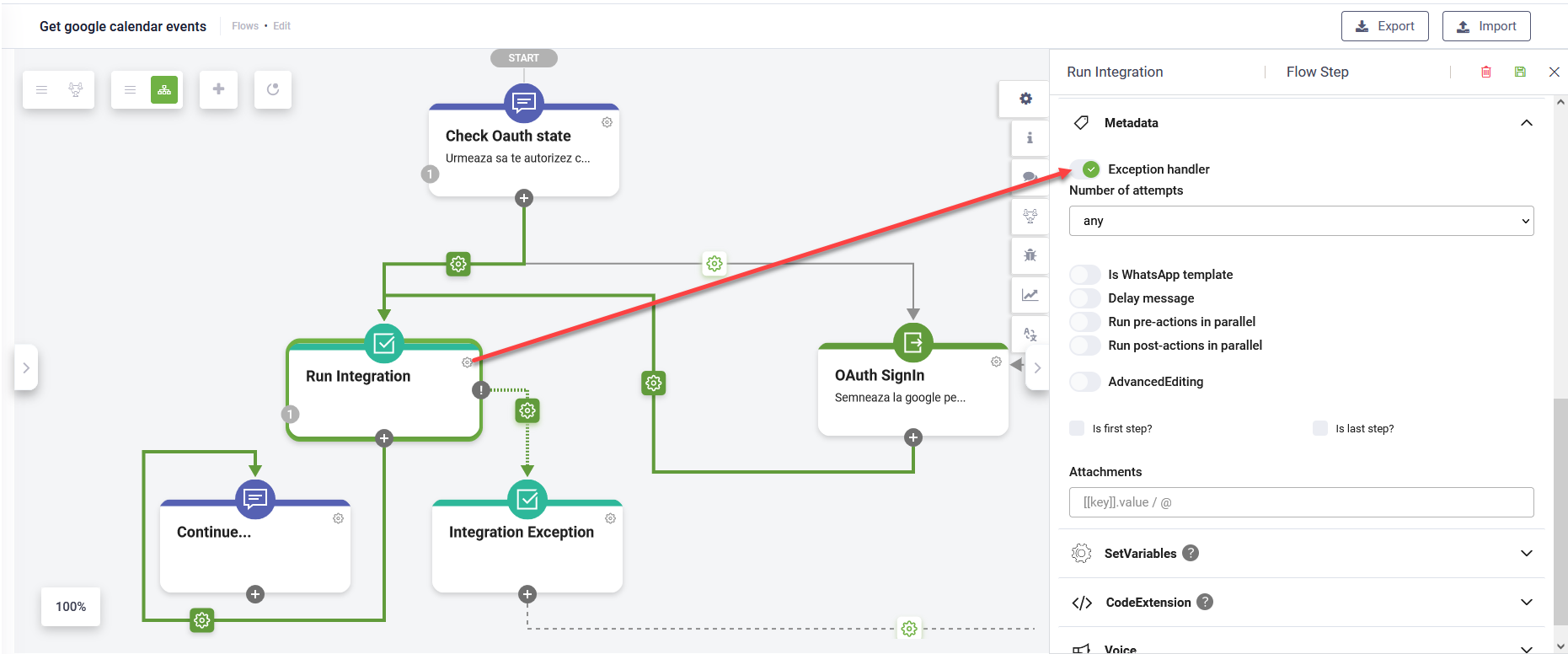
- Handle the exceptions when the access token expires. For that, on the integration step, in the Metadata section, tap on Exception handler.
- Add an action step for integration exception that is executed if [[SystemError]].IsException == true. The Oauth 2.0 Sign in flow step is executed if [[SystemError]].Code=="401".
- Continue the conversation if no exceptions are thrown during the integration execution.